An Interesting Find: STM32 RDP1 "Decryptor"
Recently while browsing Xianyu (闲鱼) looking for BYK-series chips (Sinowealth 8051 MCUs) for another project I'm working on, I stumbled across something peculiar: a device claiming to bypass STM32 RDP1 (Read-Out Protection Level 1) on F0, F1, F2 and F4 series chips. As it turns out, there's a whole market for these if you search for "STM32解密" (STM32 decryption).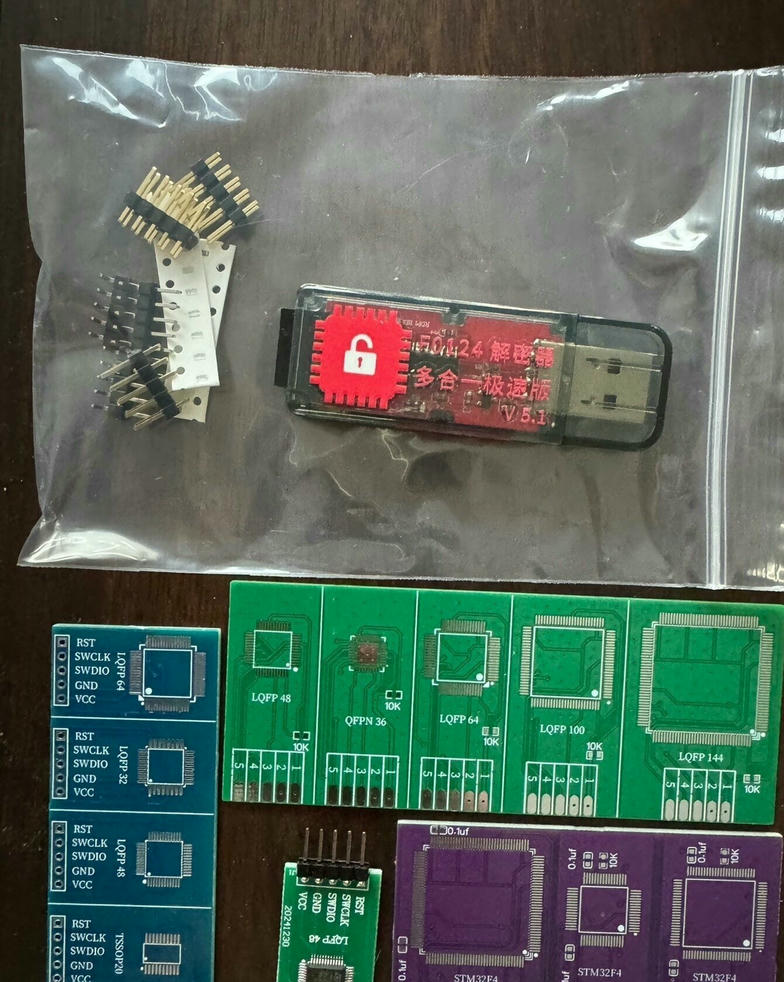
At about 150 yuan, roughly 19 EUR plus shipping and forwarding on top, I decided to bite the bullet and just buy one to see if it actually works.
What arrived§
The package contained a blue USB dongle (the programmer), two green adapter PCBs, a row of double and a row of single 2.54mm pin headers and a couple of 10K resistors.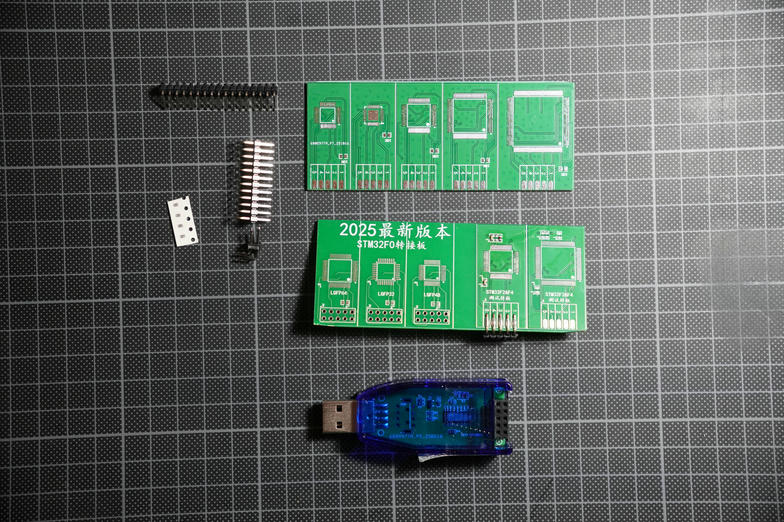
The adapter boards have footprints for the various packages of F0, F1 and F2/F4 chips, along with pads for decoupling capacitors on the necessary VCAP pins and a resistor pulling BOOT1 down. I had to supply the 0.1uF caps for the VCAP pads myself.
Testing with an STM32F205RBT6§
I had an STM32F205RBT6 lying around, so I desoldered it and placed it on the adapter board.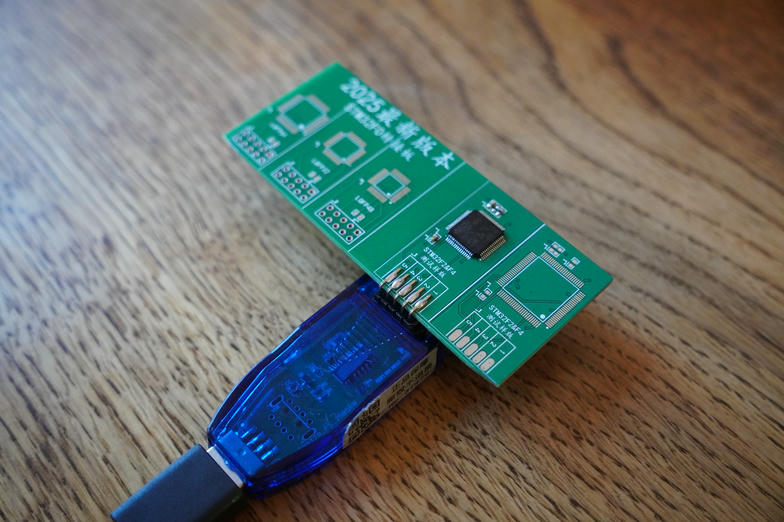
The device comes with a Windows utility. Before I could even get it running, I had to deal with a couple of hurdles. First, the software immediately triggers Windows Defender, probably for good reason. Since I was running this in a throwaway VM anyway, I just turned it off. Second, the application wouldn't launch until I changed the system encoding for non-Unicode programs to Chinese Simplified in the Windows 11 regional settings (Settings > Time & language > Language & region > Language for non-Unicode programs > Chinese (Simplified, Mainland China)).
The instructions that came with the device recommended using freeze spray on the chip during the read process. I was ready for that, but it turned out to be unnecessary in my case. It read just fine at room temperature.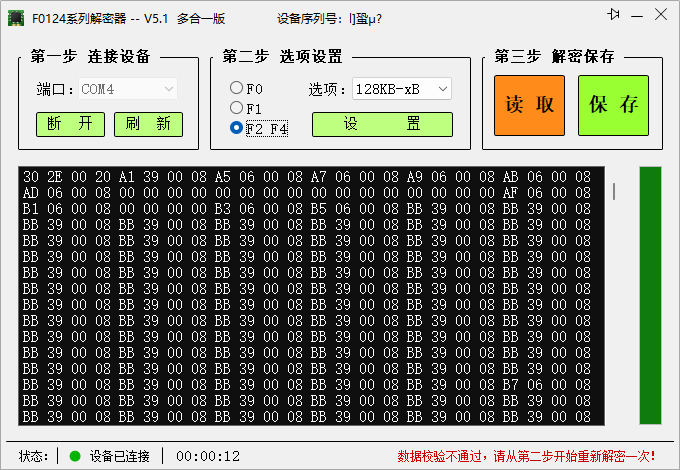
One quirk: the software would always overshoot when reading. A STM32F205RB has 128KB of flash, but the tool would happily read past that boundary, padding everything beyond it with 0xFF. The actual flash contents within the valid 128KB region were correct though, so it's easy enough to just trim the output to the right size.
Conclusion§
This thing actually works. It successfully dumped the full flash contents of an RDP1-protected STM32F205RBT6 without needing to introduce any external faults like cooling the chip down.
To be clear, this device is not the first to allow circumventing RDP1. There have already been documented ways for most of these devices: voltage glitching on STM32F4, the Exception(al) Failure debug interface exploit on STM32F1, Cold-Boot Stepping on STM32F0, and reproducible glitching setups with open-source tooling. But all of these require understanding the attack, building or buying a glitching rig, and tuning parameters. A turnkey product like this one just lets you solder the chip onto the adapter and click a button. It's both concerning and exciting.
Finally, other than glancing at the PCB, which has an SOP-16 IC with the label scraped off (presumably the microcontroller), I haven't tried analyzing how this device works yet. The Windows-only host app is not great either, but shouldn't be too hard to recreate it if someone wanted to. Might have to take a closer look at what's going on under the hood sometime. Or hopefully someone else will!